1. Location History

Image Source: Reddit
Even if you've deactivated real-time GPS tracking on your mobile device, it's essential to know that your phone might still maintain a chronological record of your movements. This location history is often accessible to you (and potentially others, like apps or services with the right permissions) through device settings. It can serve various purposes, from enhancing your user experience to aiding in criminal investigations. However, this feature also raises privacy concerns as it provides a detailed profile of your daily life, habits, and places frequented.
2. Wi-Fi Tracking

Image Source: Reddit
Turning off GPS does not necessarily make you invisible to tracking. Whenever your phone is connected to a Wi-Fi network, its location can be ascertained via that connection. This is often less precise than GPS but still relatively accurate. Public spaces like shopping malls often employ Wi-Fi tracking to monitor customer behavior and traffic patterns. This method of tracking can also be used by malicious actors if they gain control of a Wi-Fi network you join.
3. Cell Tower Pings

Image Source: Reddit
When GPS and Wi-Fi are both turned off, your phone's location can still be estimated by the cell towers it connects to. This method uses a process called "triangulation" to approximate your position. While this is not as accurate as GPS or Wi-Fi tracking, it provides a fairly good indication of your general area. Law enforcement agencies commonly use this technique during investigations.
4. Third-Party Apps

Image Source: AIKO
Android phones, including those by Samsung, often allow third-party applications to access location services, sometimes even when the app is running in the background. This could be useful for features like weather updates or food delivery, but it also poses a risk as you may not be fully aware of what data is being collected and how it's being used or stored.
5. Opt-In Features

Image Source: Solutions By Text
Many location-based services require users to "opt-in." However, people often agree to these terms without fully comprehending the extent of the tracking involved. Sometimes the language in terms of service agreements is complex and hard to understand, which can lead to uninformed consent and potential misuse of your location data.
6. Data Retention
Image Source: Dataconomy
One of the most concerning aspects of location tracking is the uncertainty surrounding data storage. It's not always clear how long your location data is kept and who has access to it. This poses potential risks regarding data breaches and unauthorized data sharing, which could expose sensitive information.
7. IMSI Catchers

Image Source: The Times
Also known as "Stingrays," these devices can intercept mobile traffic and are often used by law enforcement. IMSI Catchers act like fake cell towers and can potentially be used to track your phone's location. This type of tracking is highly controversial due to its invasive nature and potential for abuse.
8. Find My Mobile
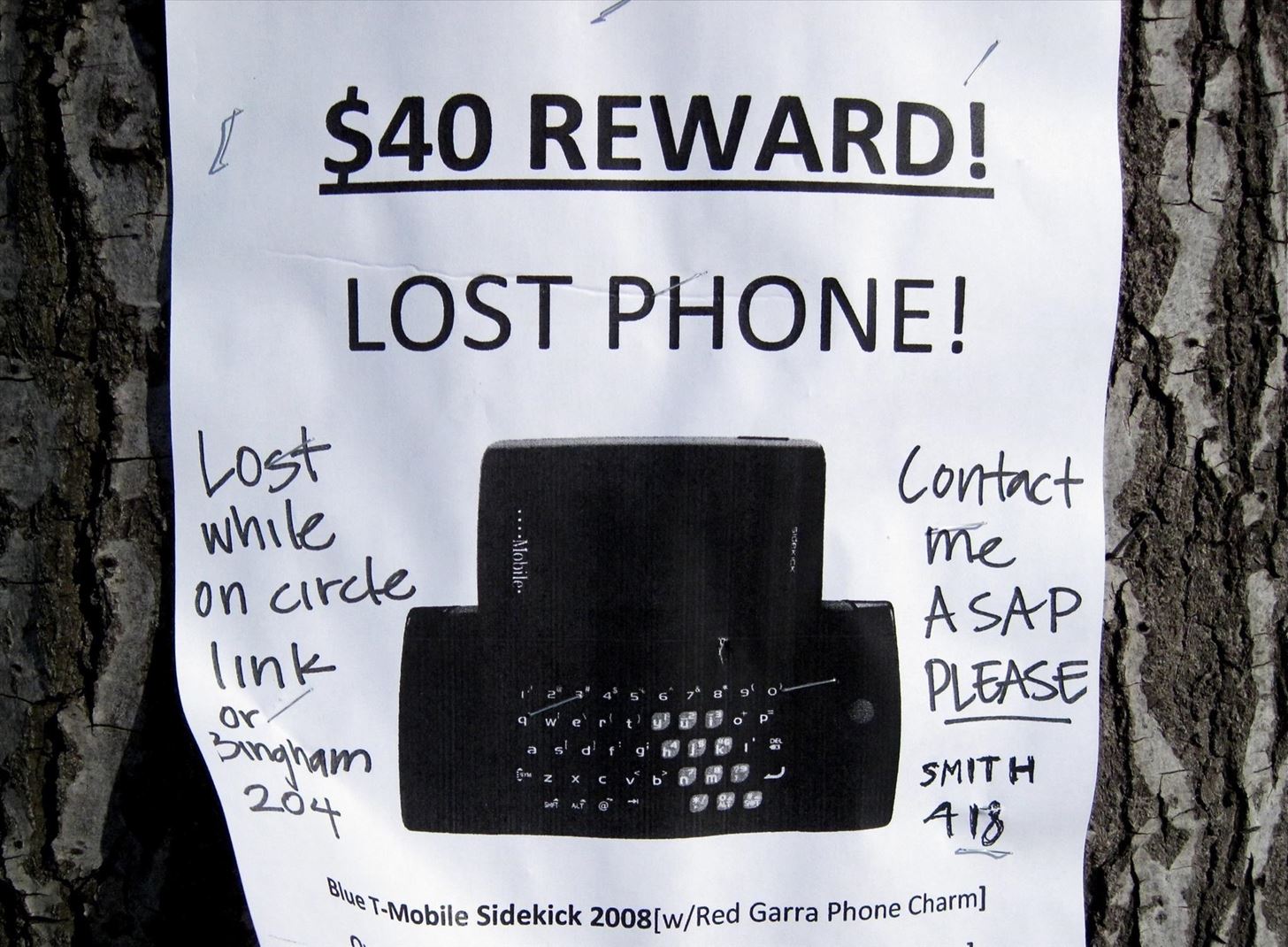
Image Source: smartphones.gadgethacks.com
Samsung's proprietary tracking service, Find My Mobile, offers more than just basic location tracking. It can remotely lock your phone, back up data, and even wipe it clean to protect your information. While beneficial for loss prevention, it also shows how much control can be exerted over your device remotely.
9. Advertisements

Image Source: Audi.com
The location data collected by your mobile device is incredibly valuable to advertisers. It allows them to target you with more personalized ads based on places you've visited or even your daily commute. This practice raises concerns about consumer privacy and the potential exploitation of personal data for commercial gain.
10. Data Brokers

Image Source: The New York Times
These are companies that collect and sell anonymized data to third parties. Your location data, once anonymized, may be included in these transactions. While this data is supposed to be non-identifiable, it's still a contentious issue, as patterns could potentially be used to de-anonymize the data, thus revealing your identity.
11. Carrier Co-operation

Image Source: The Times
Mobile carriers often have a working relationship with law enforcement agencies and may cooperate in tracking individuals under specific legal conditions, such as court orders or emergency situations. This cooperation can be controversial, as it brings up questions of civil liberties and the extent to which surveillance should be allowed. However, it can also serve important functions, like aiding in criminal investigations or finding missing persons. Regardless, it highlights the importance of understanding the scope of data carriers hold and how it can be used.
12. Device IDs

Image Source: reddit.com
Each mobile device comes with a unique identifier, such as the International Mobile Equipment Identity (IMEI) number. These identifiers can also be used for tracking purposes, whether it's for locating a lost or stolen device or for more intrusive forms of monitoring. Device IDs offer another layer of traceability, separate from traditional GPS or Wi-Fi-based methods. It's important to be aware that merely changing your SIM card will not change your device ID, leaving you susceptible to tracking.
13. Offline Tracking

Image Source: Hugh Malkin
Surprisingly, some tracking features can function even when your device is offline. In these cases, location data is typically stored locally on the device and then transmitted back to servers once an internet connection is re-established. This underscores that you can be tracked not just in real-time but also historically, creating a comprehensive record of your movements that may be analyzed or stored for later use.
14. Background Location Updates
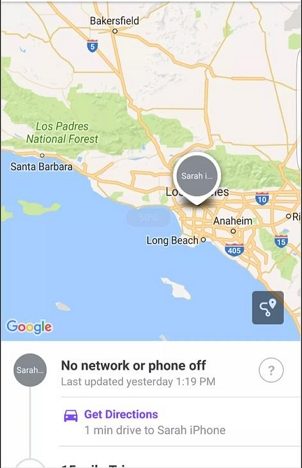
Image Source: CMC Distribution
Some applications may request or pull location updates even when they're not actively in use. This means that while you're not interacting with the app, it can still track your location in the background. This feature can be useful for things like emergency services or navigation apps, but it's crucial to understand which apps have this ability and how they're using the data they collect to avoid unintentional sharing of your location.
15. Family Sharing

Image Source: Reddit
Many smartphones now come with features specifically designed for family tracking. Parents may find these features useful for keeping tabs on their children's whereabouts. While seemingly innocent, the capability for family members to track each other’s movements introduces a host of privacy implications. This feature could potentially be misused for more nefarious purposes, such as stalking or control.
16. Sensor Data

Image Source: Nikkei Asia
Modern phones come equipped with a variety of sensors, such as accelerometers, gyroscopes, and magnetometers, that can also be used for tracking purposes. These sensors can detect movement and orientation, offering another layer of data that could potentially be used to determine your actions or behavior patterns, in addition to your location.
17. Factory Reset

Image Source: HP
A factory reset may seem like the ultimate solution to eliminate tracking features, but this isn't always the case. Some tracking mechanisms may persist even after a factory reset, particularly those deeply embedded in the device's hardware or firmware. This should serve as a reminder that it's difficult to completely "disappear" in our interconnected world.
18. Two-Factor Authentication

Image Source: Get Licensed
While primarily a security measure, two-factor authentication can also serve as a tracking method. When you receive a verification code via SMS or an authentication app, the service you're using effectively confirms your location. While the primary intent is to secure your accounts, it also demonstrates how even security measures can have tracking implications.
19. Incognito Mode

Image Source: ELEVATE EACH OTHER
Many people assume that using "incognito" or "private" modes on apps or browsers will disable tracking features, but this is not always true. Certain apps and services may still collect data or use your location despite these settings, emphasizing the importance of being aware of the capabilities and limitations of privacy features.
20. App Permissions

Image Source: British Council
When installing new apps, you're often prompted to grant various permissions, including access to your location. However, not all apps are transparent about how they will use this data, whether it will be shared, or how long it will be stored. As users, it's essential to scrutinize these permissions and consider the trustworthiness of the apps requesting them.
21. International Tracking

Image Source: Wikipedia
Different countries have varying rules and regulations concerning phone tracking, creating a complex landscape for mobile users who travel abroad. For example, some nations might have strict data protection laws that limit tracking, while others may have more lenient policies that allow for extensive surveillance. It's crucial to be aware of these regulations, especially when crossing borders, as you could unknowingly be subjected to different forms of tracking or data collection based on local laws.
22. Voice Assistants
Image Source: Obama White House Archives
Devices like Siri, Google Assistant, and Alexa sometimes use location data to provide more contextual information and enhance user experience. For instance, asking about the weather will yield a localized forecast. While convenient, this feature also means that voice assistants have access to your location data, which could be stored, shared, or used in ways that are not immediately clear to the end-user.
23. Emergency Services

Image Source: CNBC
Modern smartphones come equipped with certain tracking features that are hardwired specifically for emergency services. Features like E911 in the United States enable accurate location tracking when you make an emergency call. While designed for user safety and quicker response times, this type of always-on tracking capability does raise questions about the potential for misuse or unauthorized access to location data.
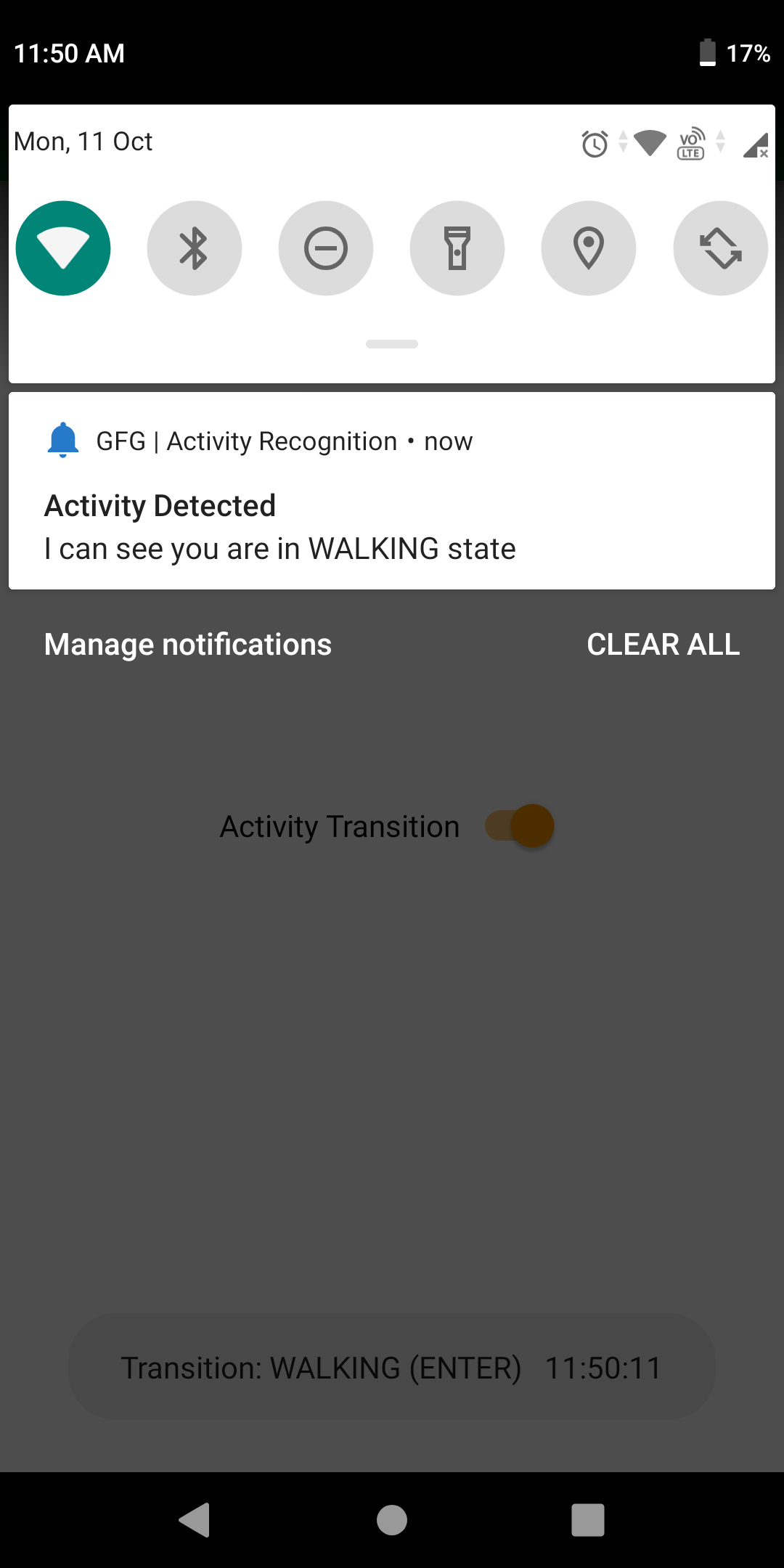
24. Activity Recognition
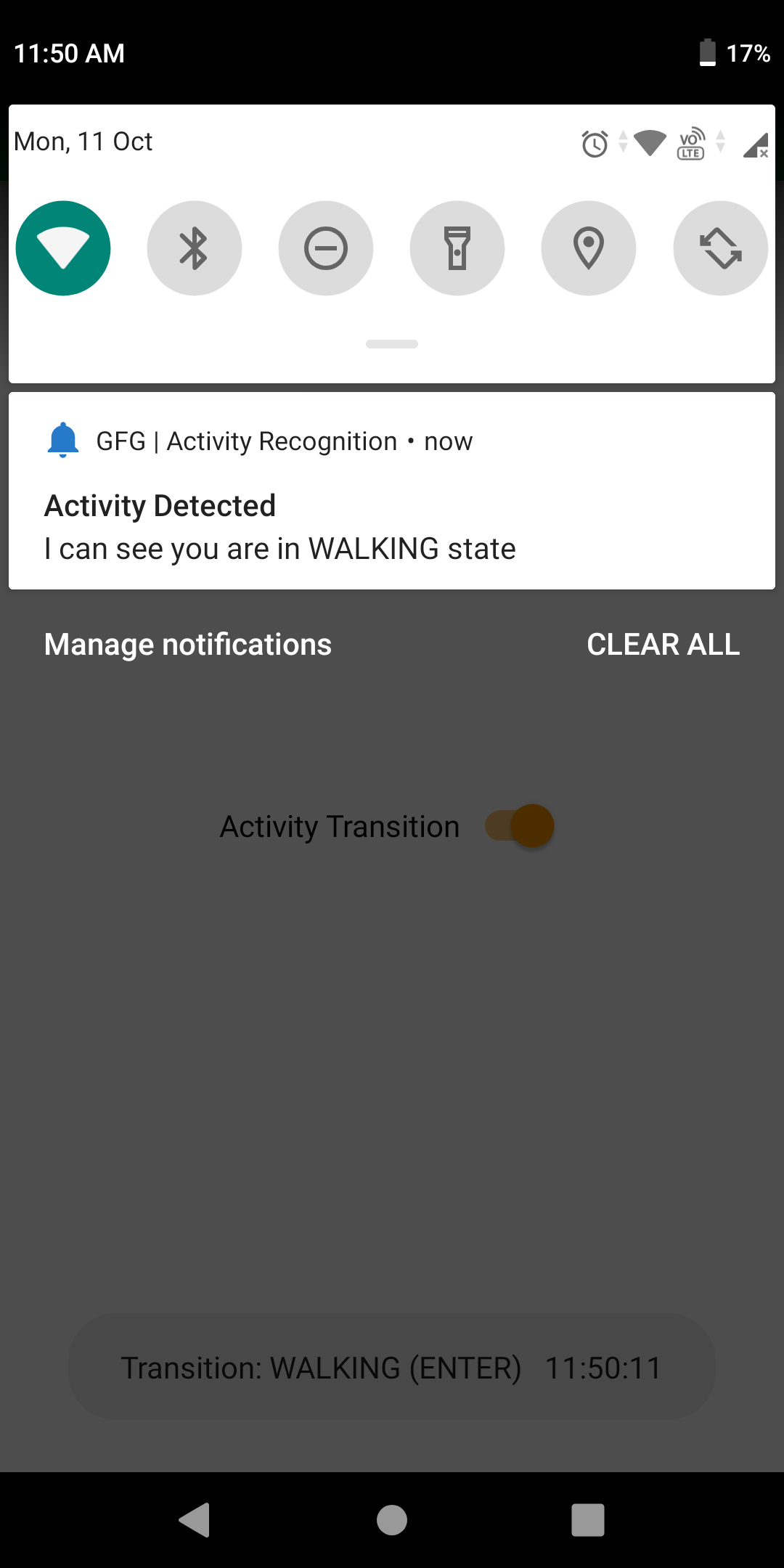
Image Source: GeeksforGeeks
Advanced sensor data in smartphones can be used to guess what you're doing, like walking, running, or driving. While this can enhance user experience in various apps, it adds another layer to what companies can discern about your daily habits and routines. This data, when collected and analyzed, could potentially be used for more invasive forms of tracking or even behavioral prediction.
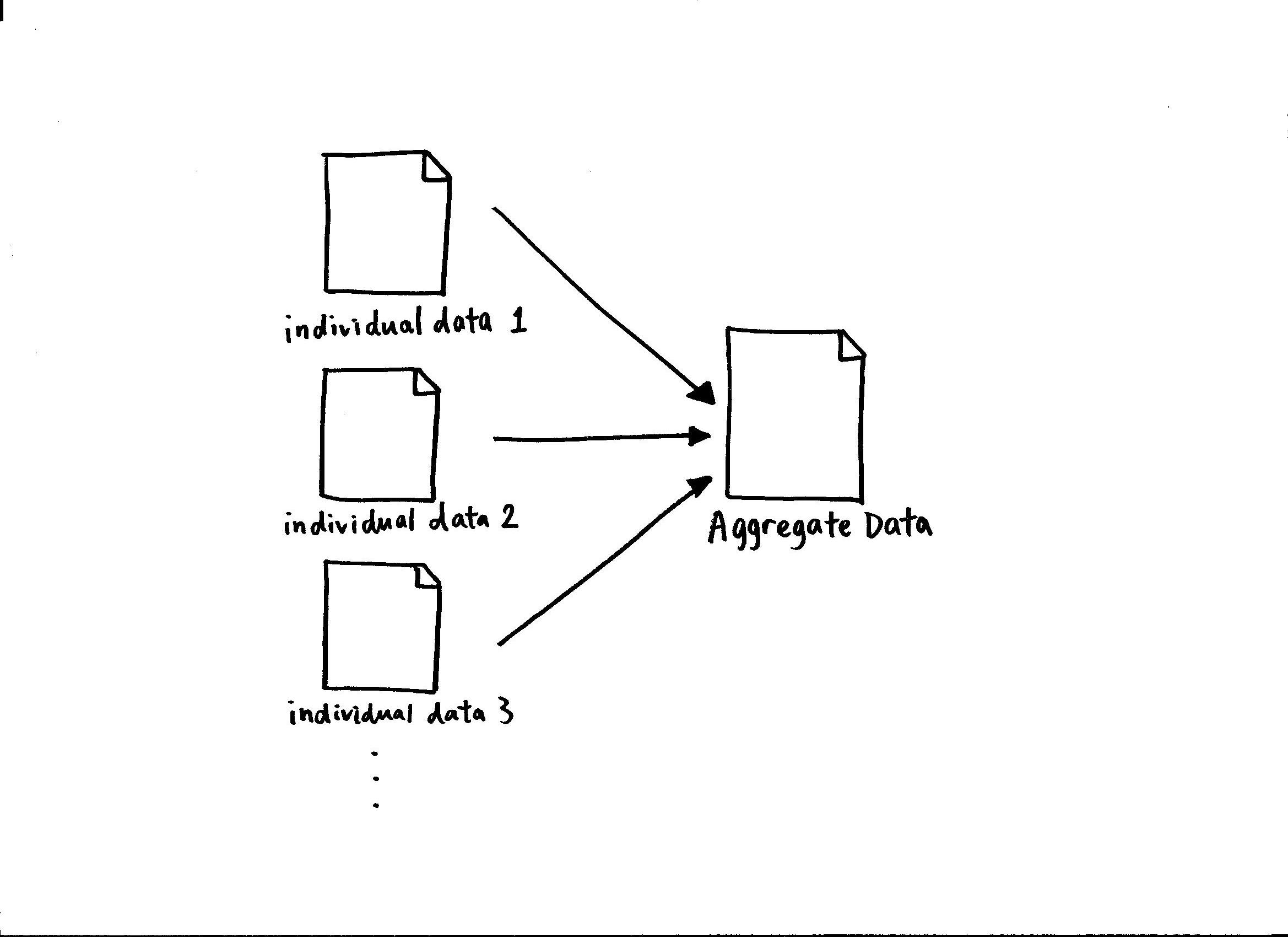
25. Data Aggregation
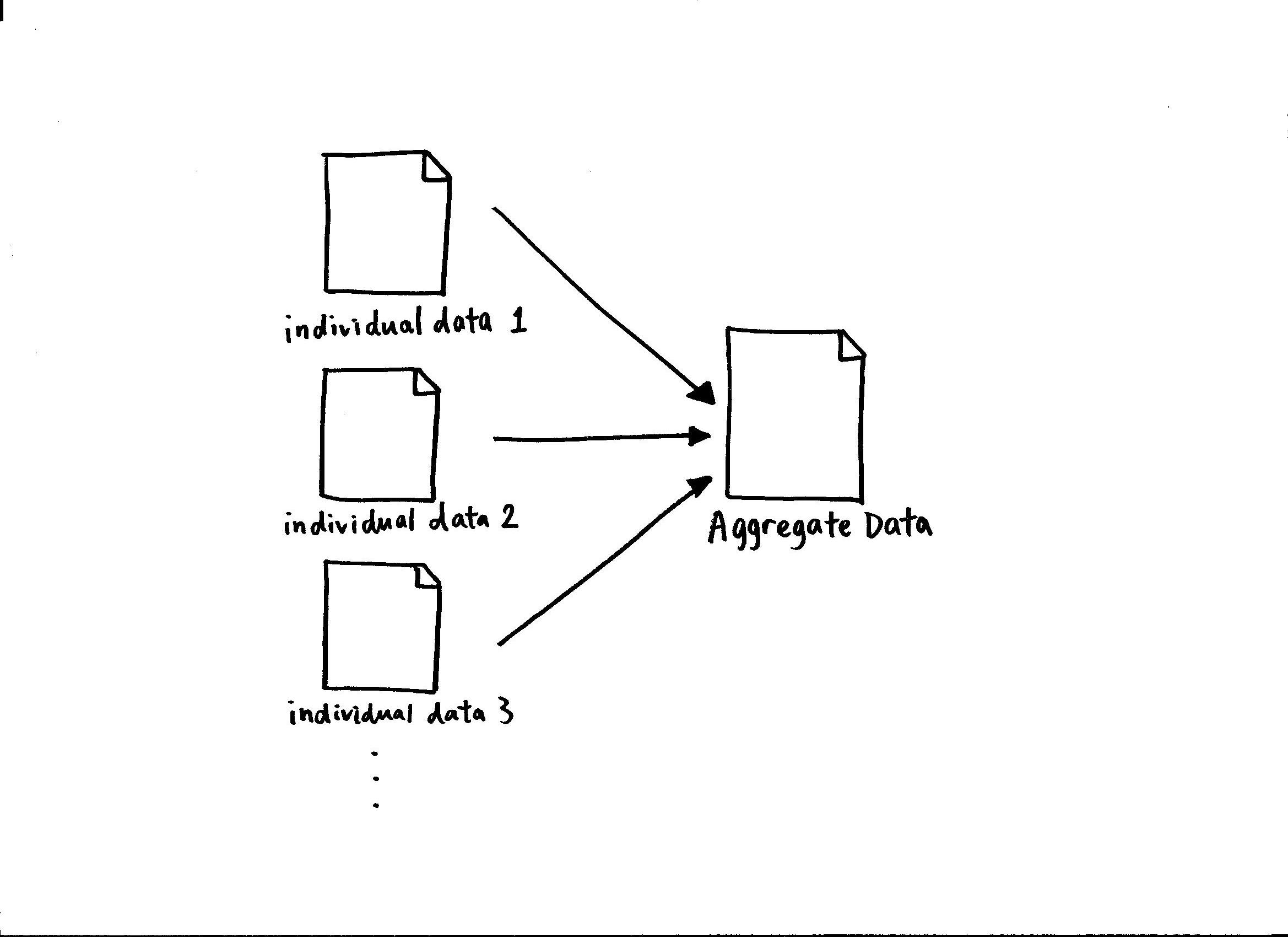
Image Source: Wikipedia
Location data doesn't exist in a vacuum. It is often combined with other types of data, such as browsing history, app usage, and social media activity, to create a more comprehensive profile of an individual. This aggregated data can be used for various purposes, including targeted advertising, analytics, and even predictive modeling, further amplifying privacy concerns.
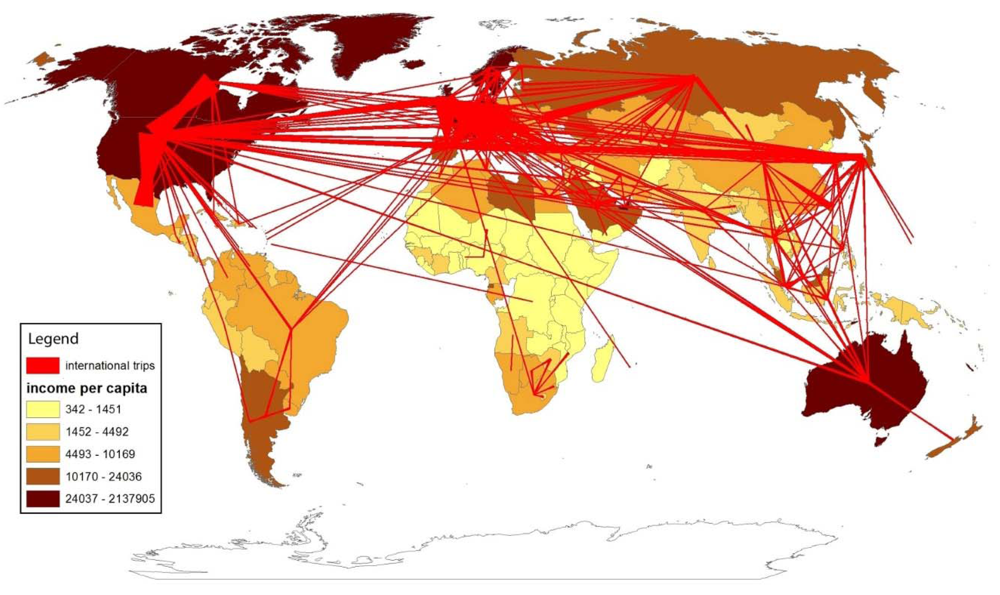
26. Travel Patterns
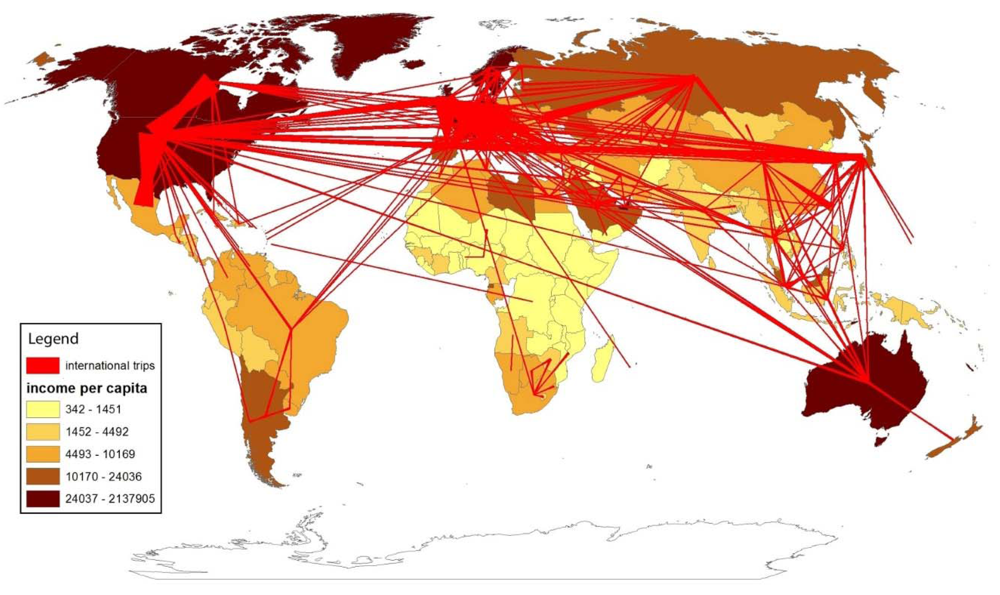
Image Source: MDPI
Algorithms are now sophisticated enough to analyze your location data and determine your common routes and destinations. This could mean identifying your workplace, your home, and other frequently visited places. While this information may be used to improve services like map apps, it could also be used for more nefarious purposes like stalking or identity theft.
27. Hidden Settings

Image Source: Shutterstock
Some mobile devices have tracking settings that are buried deep within their menus, making them hard to find and disable. This obscurity makes it challenging for average users to control what types of tracking they are subjected to, exacerbating privacy concerns and limiting user agency in managing their own data.
28. Software Updates

Image Source: Euro Weekly News
Mobile operating systems and apps are continually updated, and sometimes these updates include changes to tracking features. The changes might be added without clear notification to the user, making it important to regularly check settings and permissions to ensure that your privacy preferences are maintained.
29. Customer Service Access

Image Source: MCVO Talent Outsourcing Services
For troubleshooting and service purposes, certain employees like customer service representatives may have access to your location data. While generally used to assist you, the potential exists for misuse or unauthorized sharing of this sensitive information, underlining the importance of understanding who can access your data.
30. Legal Requests

Image Source: Vox
In extreme situations, such as criminal investigations or national security concerns, mobile carriers and service providers may be legally obligated to hand over location data to authorities. While generally governed by laws and oversight, this use of location data brings up critical ethical and legal debates about the balance between security and individual privacy.